What does ‘Office ATP Safe Attachments’ actually block?

Whenever I talk to customers about Office ATP Safe Attachments, they immediately ask me, what exactly it does protect us from. I thought it’s time to do some tests and clarify that. If you want to read more about Office ATP basics, read my other blog post.
In my tests I was using Office ATP with dynamic delivery. I was sending Emails to myself with different attachments to check how ‘Safe Attachments’ reacts. I was using Mimikatz, a self-written custom executable and a Word file that includes a little macro. So, lets first talk about macros in Word.
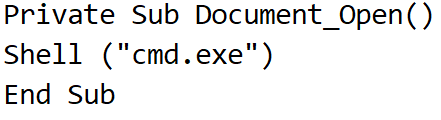
I have created a Word file that contains a small macro:
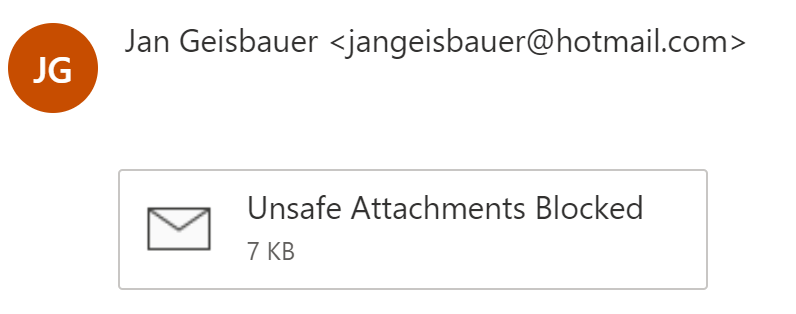
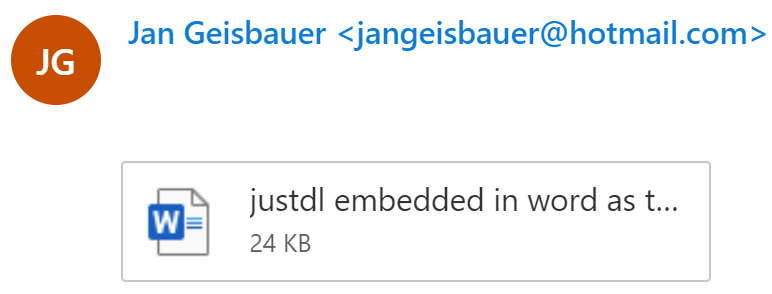
As you can see, the macro just opens a command prompt. Sending this word file through Office ATP did not bring any issues – the mail was delivered:

So, lets enhance things a little and create some powershell code within the macro to download a .cmd file from dropbox. The .cmd contains one line to create a new folder (mkdir):

No matter if you zip this or not, the attachment is not delivered to the mailbox:
Then I password protected a file with the same macro – password protecting the file basically encrypts it. The attachment was delivered since ATP had no chance to evaluate the document since it didn’t know the password:

Mimikatz
Well, this section is quite boring – and therefore short: Mimikatz zipped and renamed to txt was not delivered. Mimikatz zipped and embedded in a Word file was also blocked. The only way to get through with Mimikatz was to base64 encode it.
Self-written App
So, here it is getting more interesting. I have written a small .net console application that comes in two flavors:
Version 1 just downloads a .cmd file that creates a folder (mkdir again):

If you leave it as is or rename or zip that executable (Console Application) it will be delivered:
But then I enhanced the source code a little, so that it modifies a startup portion of the registry:
Version 2

With this adjustment I tried the following actions:
- renamed to .txt
- zipped
- renamed to txt and embedded in word
All actions led to a block:

I then re-checked the behavior and did the same (renaming, zipping and embedding in Word) with the 1st version of the custom app that just downloads a file – the attachments were delivered.
Conclusion
You can clearly see that ATP Safe Attachments is doing a detailed behavioral analysis. It can distinguish between an exe that is just downloading a file and one that is writing to some odd places in the registry.
During my tests I had to “struggle” with Windows Defender AntiVir, Windows Defender ATP and with all the security stuff in Word (“SECURITY-WARNING …”). That underlines that Office ATP Safe Attachments is just one link in the chain – which is good.
Another one is to restrict process creation from Office macros. If you prohibit those (with Exploit Guard), macros cannot start a powershell script and the like.
In the table below I have summarized the scenarios I have tested. Do you have more? Let me know by Email or in the comments, I will then update the table accordingly.
