FritzBox 2 Sentinel

As part of a bigger blog post coming up here soon, I have created a PowerShell script that connects to your FritzBox, reads its event logs, extracts the event time, IP addresses and event messages and sends everything to Azure Sentinel for comfortable hunting and alerting and basically everything else Sentinel offers.
You might ask: what is a ‘FritzBox’? To be honest, I don’t know about the global prevalence of these Internet Routers – at least in Germany, they have like 70% market share. But even if you are not using a FritzBox at home, the script might be helpful, if you want to sync your own home internet router logs to Sentinel, if you tweak it a little.
The Script
Since there are no documented APIs, we need some magic to connect to your FritzBox and get the event logs. There are several sources on the internet on how to do so. I modified the examples a little, to fit my needs:

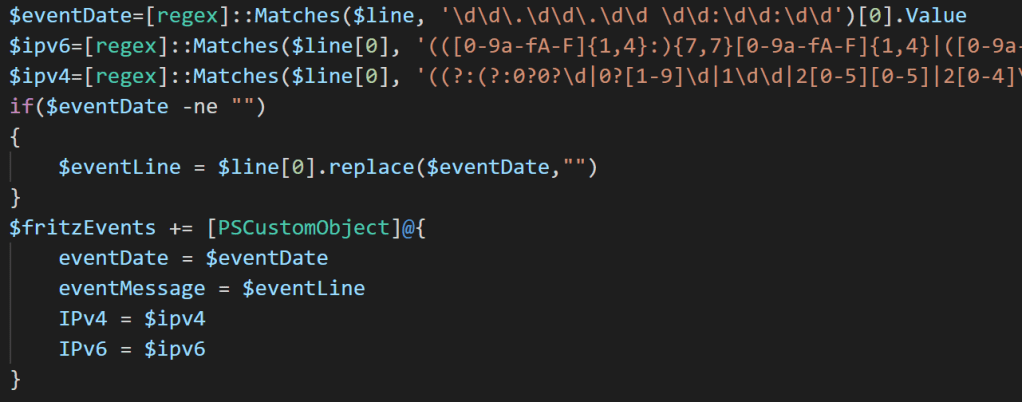
The next important part of the script then extracts the IP addresses and dates from the event message and matches it to the field names in Sentinel:
With that we can send the gathered events to Sentinel via the Data Collector API.
The Hunting Expererience
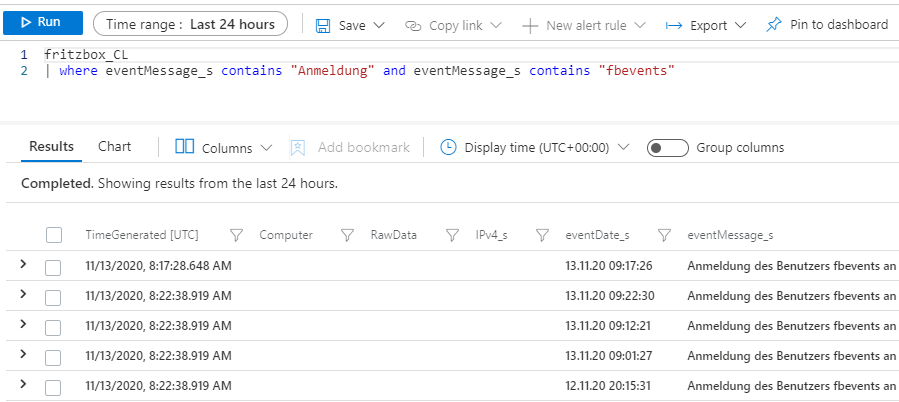
After you ran the script for the first time, in Sentinel, under ‘Custom Logs’, you will find a new table called ‘fritzbox_CL’. Underneath this table, you will find our in the script defined fields, which we extracted from the raw event messages (eventDate, eventMessage, IPv4 and IPv6).

With that you can e.g. hunt for logins from specific users (“Anmeldung == Login” // UserName == fbevents):
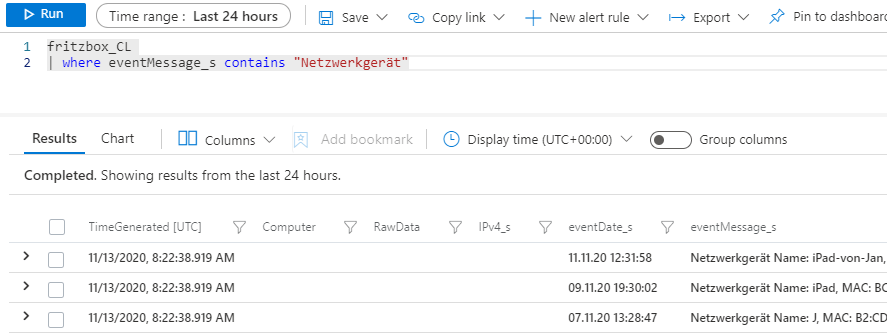
Or you can search for “wrong password” within the event message. You can also hunt for new network devices (“Netzwerkgerät”) connecting to your home net:
If you schedule the script on a small ‘server’ in your home net, you always get the latest events and of course, you can even create analytic rules from your hunting queries and get alerted by a playbook to not miss that your daughter has turned on her iPad 😉
Find the script on GitHub.
Happy Hunting!