Alertrule from github to Azure sentinel

The Azure Sentinel community is great. Many people contribute to the Azure Sentinel GitHub site. Rod Trent wrote an article on how to deploy analytic rules from GitHub to your Sentinel instance. This is great, however, the rules are written in YAML and can therefore easily be imported programmatically.
I have written a short PowerShell function for that purpose. Let’s check the workflow:
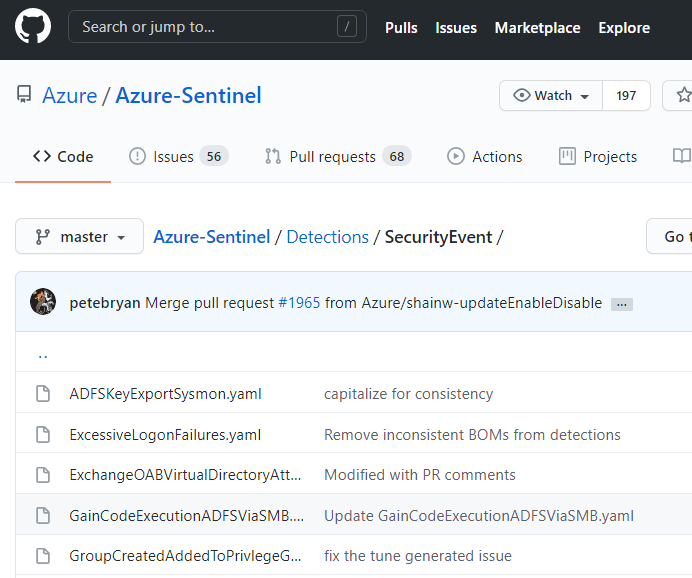
Browse to the Sentinel repo: https://github.com/Azure/Azure-Sentinel/tree/master/Detections
Click on your a detection query, then click on raw:

Copy the raw URL and save it somewhere temporarily. Now, in Sentinel, click on Settings / Workplace Settings and note the resource group and the workspace name.
That’s all we need. Now lets start the with the script from GitHub.
import-module .\alertRuleFromGHToSentinel.ps1
New-AzSentinelAlertRuleFromGitHub -resourceGroupName "resource group name" -workspaceName "workspace name" -gitHubRawUrl "https://raw.githubusercontent.com/Azure/Azure-Sentinel/master/Detections/SecurityEvent/NOBELIUM_SuspiciousRundll32Exec.yaml"Next, you will be prompted for authentication and then the alert rule will be created based on the criteria specified in the yaml file:

Back in Sentinel, the Rule has been created for you …

… with the paramters from the yaml file.
Of course, you can edit the rule to meet your needs:

UPDATE 18-March-2021
Since you asked for it: this function now also supports batch-mode. For that you have to set -isGitHubDirectoryUrl to $true and specify the Sentinel GitHub Repo URL of a directory beneath “Detections”:
New-AzSentinelAlertRuleFromGitHub -resourceGroupName "rg-name" -workspaceName "ws-name" -gitHubRawUrl "https://github.com/Azure/Azure-Sentinel/tree/master/Detections/SecurityEvent" -isGitHubDirectoryUrl $true
With this you can easily create like 30 rules from a directory in the repo in a few minutes.
Happy Hunting!
Pingback: How to Import One or Multiple Analytics Rules into Azure Sentinel – Azure Cloud & AI Domain Blog
hello after install/import of the module, getting error:
New-AzSentinelAlertRuleFromGitHub : The term ‘New-AzSentinelAlertRuleFromGitHub’ is not recognized as the name of a cmdlet, function, script
file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct and try again.
At line:1 char:2
+ New-AzSentinelAlertRuleFromGitHub -resourceGroupName “prd-threatdect …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : ObjectNotFound: (New-AzSentinelAlertRuleFromGitHub:String) [], CommandNotFoundException
+ FullyQualifiedErrorId : CommandNotFoundException
LikeLike
Check my exact description above. You first have to run the ps by . .\alertRuleFromGHToSentinel.ps then the function is known to the system. Let me know if you got it working. Thanks
LikeLike
Hi, first thanks for making this. But I’m also getting the same error message:
PS /Users/john> ./alertRuleFromGHToSentinel.ps1
Module Az.SecurityInsights exists
Module powershell-yaml exists
PS /Users/john> New-AzSentinelAlertRuleFromGiHub -resourceGroupName “xxxxx” -workspaceName “xxxx” -gitHubRawUrl “https://raw.githubusercontent.com/Azure/Azure-Sentinel/master/Detections/ThreatIntelligenceIndicator/FileHashEntity_SecurityEvent.yaml”
New-AzSentinelAlertRuleFromGiHub: The term ‘New-AzSentinelAlertRuleFromGiHub’ is not recognized as a name of a cmdlet, function, script file, or executable program.
Check the spelling of the name, or if a path was included, verify that the path is correct and try again.
PS /Users/john> New-AzSentinel
New-AzSentinelAlertRule New-AzSentinelDataConnector New-AzSentinelIncidentComment
New-AzSentinelAlertRuleAction New-AzSentinelHuntingRule New-AzSentinelIncidentOwner
New-AzSentinelBookmark New-AzSentinelIncident
LikeLike
Pingback: How to Import One or Multiple Analytics Rules into Azure Sentinel – Azure Sentinel News
Hi John, you forgot one dot – check my exact description above … 🙂
LikeLike
Thanks, works like a charm!
LikeLike
i’m getting
New-AzSentinelAlertRuleFromGitHub:
Line |
68 | New-AzSentinelAlertRuleFromGitHub
| ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
| You cannot call a method on a null-valued expression.
Can you help please ??
LikeLike
Hi Tom, please paste the command line, you are using here … thanks
LikeLike
$rg = “rg-sentinel”
$wks = “sentinel-1”
. .\alertruletosentinel.ps1
New-AzSentinelAlertRuleFromGitHub -resourceGroupName $rg -workspaceName $wks -gitHubRawUrl “https://github.com/Azure/Azure-Sentinel/tree/master/Detections/SecurityEvent” -isGitHubDirectoryUrl $true
thanks Jan
LikeLike
Hey Tom, looks fine for me what you are doing here. I updated the script in GH zu include some high-level “debugging” status info. It will print out the URLs it finds etc. Use the new version and see if something comes back. You get the auth request? (a browser window should open and you would need to auth with an account with permissions in your Sentinel.) ALSO: I have updated the blogpost above and changed . .\alertRuleFromGHToSentinel.ps1 to import-module .\alertRuleFromGHToSentinel.ps1, since this seems to confuse lots of people …
LikeLike
The import of a single rule works fine for me, but using the syntax above batch mode runs and just seems to sit there and hang?
Anyone had any success with batch mode import?
LikeLike
Hi Paul – please paste the command line, you are using here …
LikeLike
New-AzSentinelAlertRuleFromGitHub -resourceGroupName rg-xxx -workspaceName la-xxx -gitHubRawUrl “https://github.com/Azure/Azure-Sentinel/tree/master/Detections/OfficeActivity” -isGitHubDirectoryUrl $true
LikeLike
looks good, so somewhere an auth window should pop up where you would have to auth against Azure. Have you seen this?
LikeLike
Yup – The auth window pops up – the behaviour is the same as if I import a single rule (which works), but that when I try the batch command (as above) it accepts the command and nothing appears to happen – no errors are returned. Yet when I import a single rule it works and the output displays the detail of the rule that was imported
Thanks for any assistance – if I can get this working it will be a massive timesaver
LikeLike
just imported all the rules from the OfficeActivity URL as you stated it. Its working for me as intended. Do you have the latest version of the script from GH?
LikeLike
Yup – I’m using the one that was committed 7days ago. Strange that it works perfectly for you. I’ll ask my colleagues to try in their tenants and see if my tenant is the anomaly.
LikeLike
I uploaded a new version. I made it a little bit more chatty – let me know, were it stops now …
LikeLike
Thanks so much for this.
Its gets as far as displaying the following:
onnect to Azure Account …
get existing alert rules …
True was set to true getting all URLs on page …
It hangs at this point.
LikeLike
then I would assume the invoke-webrequest is not working somehow. Try: Invoke-WebRequest “https://github.com/Azure/Azure-Sentinel/tree/master/Detections/OfficeActivity” in the powershell window … is that working? If not – maybe your IE was never started than try the “-usebasicparsing” switch in PowerShell5 or maybe you have a proxy in between …
LikeLike
HI that works grate thanks
I can see some people having issue If they are connected to multiple Azure subscriptions, you may so they may want to change the following to line 40
Connect-AzAccount -Tenant ‘ID ‘ -SubscriptionId ‘ID’
And bind it to a subscription and have a script per subscription
LikeLike
I tried this but I could never get it to work. I added the line, put in the Tenant ID and Subscription ID but nothing changed.
LikeLike
Hi, I get the error “Cannot bind argument to parameter ‘existingRules’ because it is null. Can u not use this script if there aren’t any rules already in place?
LikeLike
never tried 🙂
LikeLike
Having a few issues with the script:
PS> New-AzSentinelAlertRule -resourceGroupName “rg-securityoperations” -workspaceName “LAW-SecurityOperations” -gitHubRawUrl “https://github.com/Azure/Azure-Sentinel/tree/master/Detections/AzureDevOpsAuditing” -isGitHubDirectoryUrl $true
I get:
New-AzSentinelAlertRule: A parameter cannot be found that matches parameter name ‘gitHubRawUrl’.
When I first started I downloaded the script from your github and ran the script ./alertRuleFromGHToSentinel.ps1 and also tried Import-Module ./alertRuleFromGHToSentinel.ps1
LikeLike
resolved
LikeLike
This is really useful, is there an option to execute somethiing similar for Hunting Queries?
Thanks!
LikeLike
I’m not great with PS and have run into a problem. I have multiple subscriptions so get WARNING: TenantId ‘zzzzzz’ contains more than one active subscription. First one will be
selected for further use. To select another subscription, use Set-AzContext.
I tried to use Set-AZcontext with my subscription name in various location in the script. However still never works, seems to bomb out with :-
New-SingleAlertRuleFromGitHub : Cannot bind argument to parameter ‘existingRules’ because it is null.
At C:\Intel\alertRuleFromGHToSentinel.ps1:63 char:150
+ … rkspaceName -gitHubRawUrl $gitHubRawUrl -existingRules $existingRules
LikeLike
Pingback: How to Import One or Multiple Analytics Rules into Microsoft Sentinel - Azure Cloud & AI Domain Blog
If anybody is facing errors while importing single analytic rule using RAW url as described in the article, follow the steps given below:
It works flawlessly and already tested in my own environment.
Million thanks to the owner for developing this script. Amazing work done!
LikeLike